About Yashus Networks.
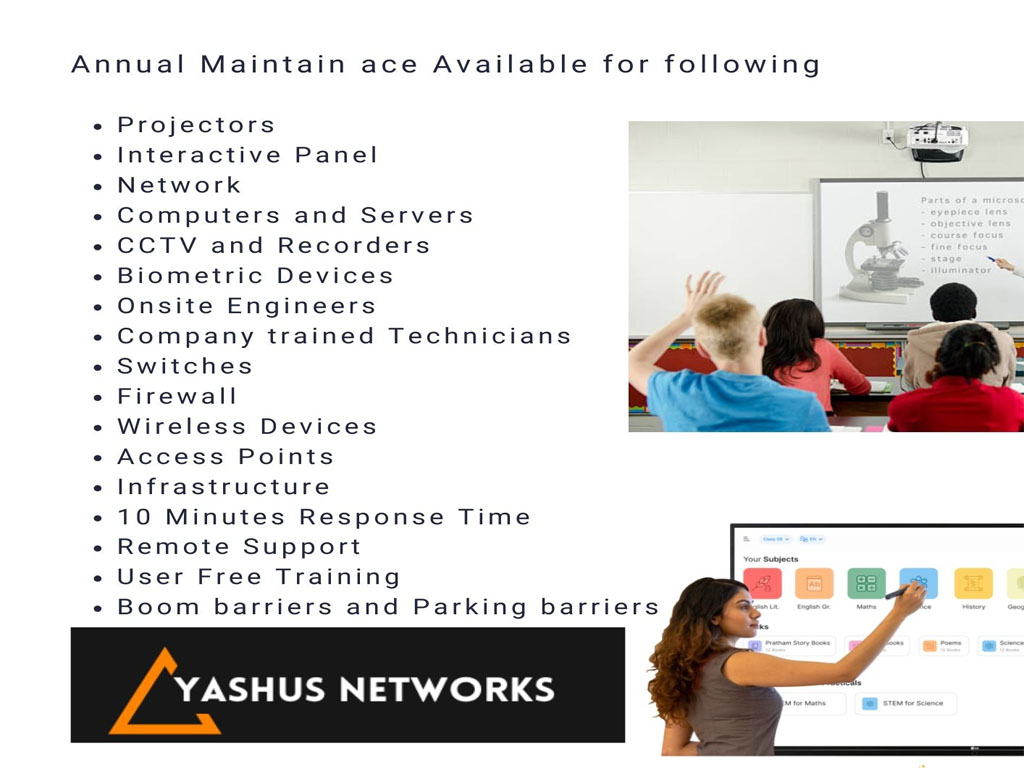
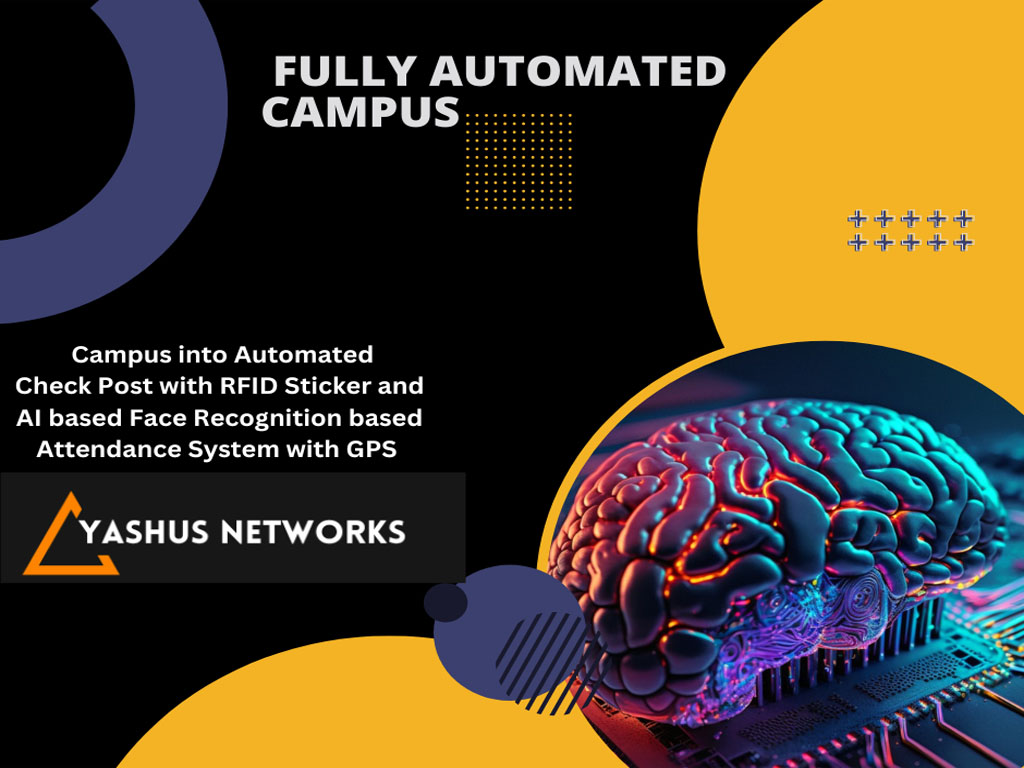
We understand that every business is unique, which is why we tailor our solutions to meet your specific needs. Our process includes Assessment: Conducting a thorough evaluation of your current network security posture. Strategy Development: Crafting a customized security plan based on your business objectives and risk profile.
Implementation: Deploying state-of-the-art security technologies and protocols to protect your network. Continuous Monitoring and Support: Providing 24/7 monitoring and support to ensure ongoing protection and peace of mind..
Expertise: Our team comprises certified professionals with extensive experience in network security. Proven Track Record: We have successfully secured networks for businesses across various industries. Client-Centric Approach: We prioritize building long-term relationships with our clients by providing exceptional service and support.